5. Reverse Engineering Models from Legacy Code#
Model-based design technology can also play an important role with regard to legacy systems. Such systems are often poorly documented and very difficult to modify to meet evolving system requirements due to the fragile nature of the underlying code. It would benefit developers to have a precise and unambiguous model of the behavior of a legacy system for which they were responsible. Such a model would serve as a formal and executable specification of the legacy system, thereby facilitating system maintenance, documentation, and evolution. The focus of this section is on how Reactis can indeed be used to derive, or reverse engineer, models from code.
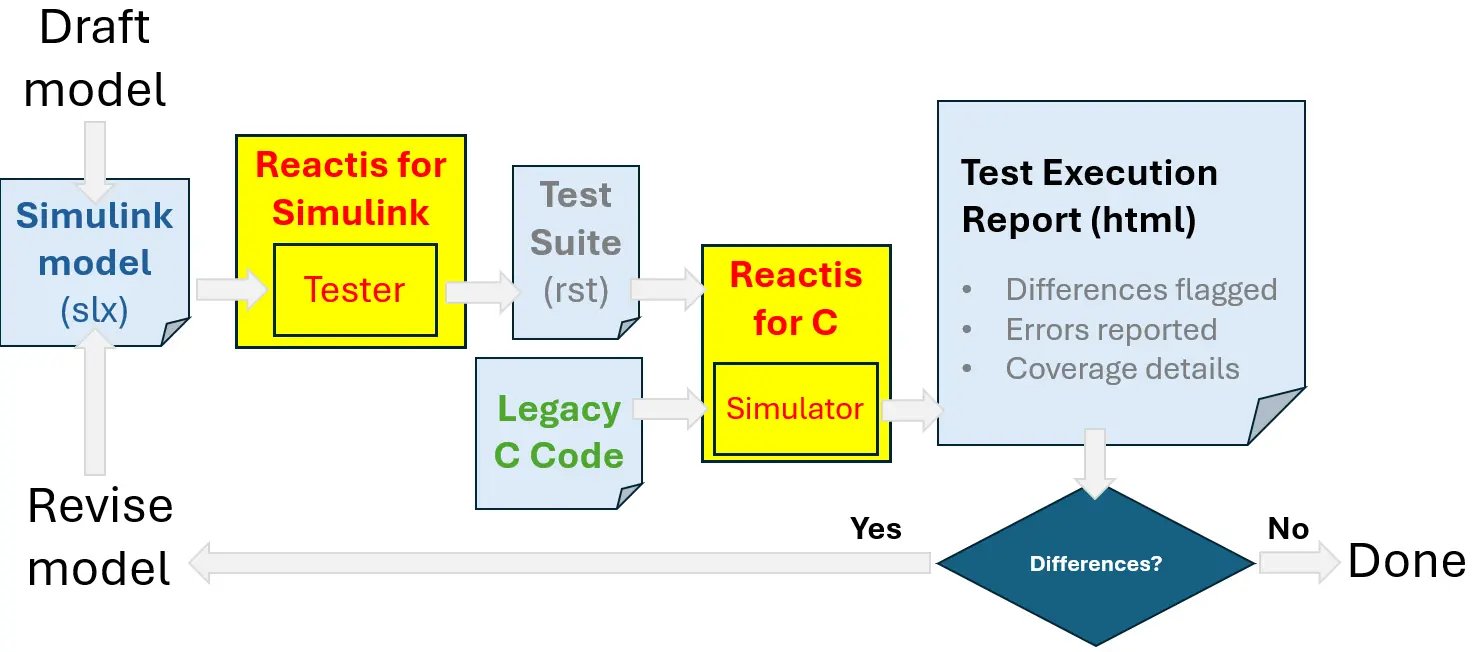
Fig. 5.1 Reverse engineering models from legacy code using Reactis.#
Figure 5.1 illustrates the process one would follow in order to use Reactis to reverse engineer models from legacy code. Reverse engineering proceeds as follows.
The Simulink / Stateflow modeling environment is used to draft a model of the legacy code.
The resulting .slx file is fed into Reactis Tester which then automatically generates a test suite from the model. The result is an .rst file (a Reactis test-suite file). The generated test suite thoroughly exercises the draft model according to various coverage metrics. Example coverage metrics include Stateflow state and transition coverage, Simulink branch coverage, and MC/DC coverage. Tester also eliminates redundancy in the test suite it generates in order to eliminate unnecessary test steps.
Reactis Simulator may then be used to visualize the execution of the tests produced by Reactis Tester, and also to fine-tune the test suite to further improve model coverage.
The test suite is then read and executed on the legacy code by Reactis for C.
By comparing the outputs produced by the software and the model on the tests in the test suite, deviations in the behavior of the model from the legacy code are readily detectable and can be used to guide the user in refining the model to ensure that it faithfully captures the behavior of the legacy system.
Reverse engineering of the model concludes when the code passes all tests generated from the model.
The beauty of having a model to go along with a legacy system is that the model serves as a formal and executable specification of the code, thereby easing the tasks of code maintenance, documentation, and evolution.